Threat Watch
Threat Watch delivers rapid insights into your cybersecurity health by identifying compromised accounts and critical.
Visit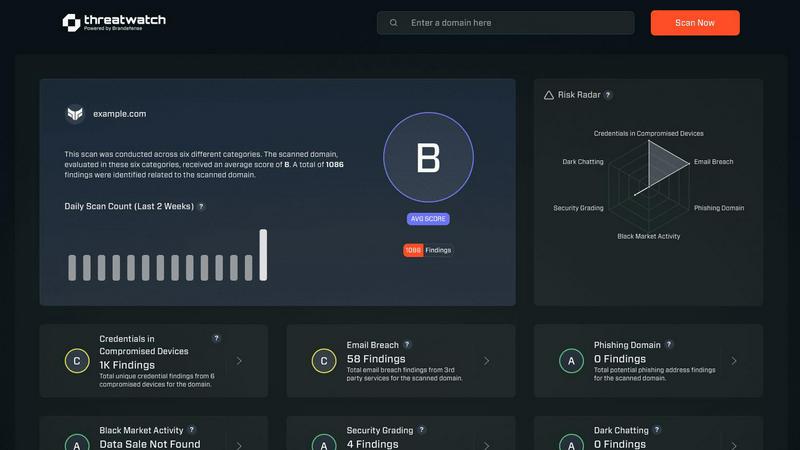
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution designed to equip organizations with the tools necessary to protect their digital assets. By providing a detailed analysis of critical security categories, Threat Watch empowers businesses to assess their cybersecurity posture effectively. This platform caters to enterprises of all sizes, enabling IT and security professionals to pinpoint vulnerabilities, exposures, and overall risk levels within their environments. The main value proposition of Threat Watch lies in its ability to deliver real-time insights coupled with automated assessments. This capability allows organizations to respond swiftly and effectively to potential threats, thereby minimizing the risk of data breaches and other cybersecurity incidents. Key features include monitoring for compromised credentials, breached accounts, phishing addresses, and dark web contents, all of which contribute to a unified approach to cybersecurity that not only enhances productivity but also improves return on investment (ROI) for organizations.
Features of Threat Watch
Real-Time Monitoring
Threat Watch provides real-time monitoring of compromised credentials, allowing organizations to stay ahead of cyber threats. This feature ensures that businesses are alerted immediately when their sensitive information is at risk, enabling proactive measures to mitigate potential damage.
Comprehensive Risk Assessment
The platform delivers automated risk assessments across critical security categories, giving organizations a thorough understanding of their cybersecurity health. This comprehensive evaluation helps prioritize vulnerabilities, ensuring that resources are allocated effectively to areas that require immediate attention.
Dark Web Intelligence
With Threat Watch's dark web monitoring capabilities, organizations can uncover threats lurking in hidden corners of the internet. This feature tracks exposed data and compromised accounts, empowering businesses to take corrective actions before their information is exploited by cybercriminals.
Phishing Detection and Response
Threat Watch includes advanced phishing address monitoring, identifying potential phishing threats in real time. By alerting organizations to suspicious addresses and behaviors, this feature helps prevent financial losses and data breaches caused by phishing attacks.
Use Cases of Threat Watch
Enhancing Security Posture
Organizations can utilize Threat Watch to enhance their overall security posture. By continuously monitoring for vulnerabilities and exposures, businesses can implement timely measures to protect their assets and reduce their risk profile.
Incident Response Optimization
In the event of a security breach, Threat Watch enables IT teams to respond rapidly by providing real-time insights and assessments. This capability not only speeds up incident response times but also minimizes the impact of breaches on business operations.
Compliance and Regulatory Adherence
Companies can leverage Threat Watch to ensure compliance with industry standards and regulations. By maintaining a comprehensive overview of their cybersecurity health, organizations can demonstrate their commitment to protecting sensitive data and adhering to legal requirements.
Employee Training and Awareness
Threat Watch can be instrumental in employee training programs by providing insights into current threats, such as phishing attempts. By educating staff on these threats, organizations can foster a culture of cybersecurity awareness, reducing the likelihood of successful attacks.
Frequently Asked Questions
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for enterprises of all sizes, from small businesses to large corporations. Any organization seeking to enhance its cybersecurity posture and protect its digital assets can benefit from this solution.
How does Threat Watch monitor dark web contents?
Threat Watch employs advanced algorithms and intelligence sources to monitor the dark web for compromised credentials and other sensitive information. This proactive approach helps organizations identify threats before they can be exploited.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to integrate seamlessly with a variety of existing security tools and platforms. This ensures that organizations can enhance their cybersecurity efforts without disrupting their current workflows.
How quickly can I expect to see results from Threat Watch?
Organizations can expect to see results almost immediately upon implementation. The real-time monitoring and automated assessments provided by Threat Watch deliver actionable insights that can help improve cybersecurity health from day one.
Explore more in this category:
Similar to Threat Watch
Effortlessly create unique and memorable business names with our AI Business Name Generator, designed to elevate your brand's identity.
MarketWrk automates CPG pricing, MAP monitoring, and reviews, transforming data into actionable insights for faster decision-making.
Opal44 translates complex GA4 data into plain English insights that boost productivity and ROI.
Fusedash transforms raw data into actionable dashboards and reports to accelerate team productivity.
Finban streamlines liquidity planning, empowering confident decisions on hiring, taxes, and investments without Excel.
Zignt automates secure contract signing with unlimited templates and no per-document fees.
aVenture provides institutional-grade venture intelligence to research startups and track market opportunities.
iGPT converts email data into secure, actionable insights to boost productivity and streamline enterprise workflows.
