Perkoon vs Phishly
Side-by-side comparison to help you choose the right AI tool.
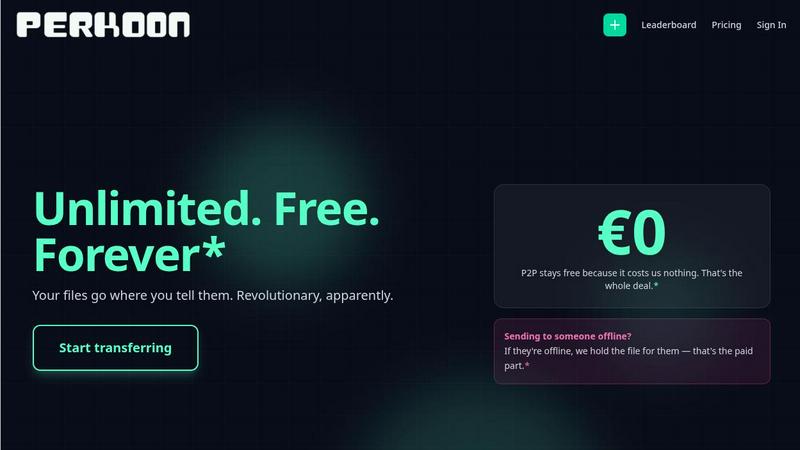
Perkoon enables unlimited, free peer-to-peer file transfers with no signup required.
Last updated: March 4, 2026
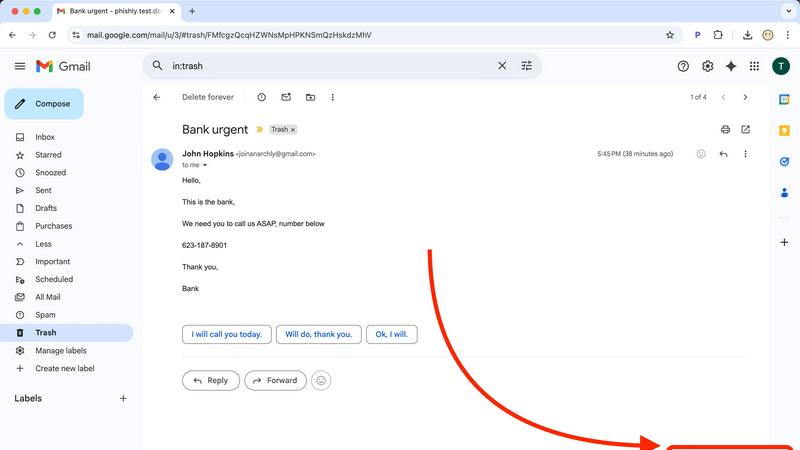
Phishly
Phishly leverages AI to swiftly detect phishing emails, enhancing security and productivity for Gmail users.
Visual Comparison
Perkoon
Phishly
Feature Comparison
Perkoon
Unlimited Free P2P Transfers
Perkoon's flagship feature utilizes WebRTC-based peer-to-peer technology to facilitate direct browser-to-browser file transfers. This method imposes no file size limits, requires no user accounts, and ensures maximum privacy and speed as data never transits a central server. For businesses, this means zero-cost transfer of large datasets, video productions, or software builds between online collaborators, directly reducing operational expenses associated with data egress and premium service tiers.
Encrypted Cloud Storage for Offline Recipients
When immediate transfer is not possible, Perkoon provides secure, encrypted cloud storage as a paid service. Files are held securely until the recipient is available, with pricing transparently covering server infrastructure costs. This hybrid model guarantees delivery reliability without forcing users into a one-size-fits-all subscription, allowing businesses to pay only for the storage and bandwidth they actually consume.
Native AI & Automation Integration
Unlike legacy services, Perkoon is built with machine-to-machine interaction as a first-class citizen. It exposes a dedicated JavaScript object (window.__perkoon) and CLI tools, enabling AI agents and automation scripts to interact with the service programmatically. This eliminates the need for unreliable DOM scraping, allowing enterprises to seamlessly integrate secure file transfer into CI/CD pipelines, automated reporting systems, and AI-driven content workflows.
Privacy-First Data Governance
Perkoon enforces a strict policy of non-interference with user data. P2P transfers are inherently private, and all cloud-stored files are encrypted. The company explicitly does not scan, analyze, or sell user data for advertising. This commitment provides legal and compliance teams with assurance regarding data sovereignty and adherence to stringent regulatory frameworks like GDPR, mitigating corporate risk.
Phishly
AI-Powered Phishing Detection
Phishly utilizes cutting-edge artificial intelligence to analyze emails for various phishing indicators. This includes identifying suspicious domains, urgent language, and spoofed sender addresses, ensuring that users receive accurate assessments of potential threats.
Risk Assessment Classification
Upon scanning an email, Phishly provides a clear risk assessment categorized into Safe, Medium Risk, or High Risk. This classification helps users quickly understand the level of risk associated with an email, enabling them to take appropriate action.
User-Friendly Interface
The Phishly Chrome extension and web tool are designed with user experience in mind. With simple navigation and straightforward instructions, users can easily scan emails without needing any technical knowledge, making it accessible for everyone.
Privacy-Focused Analysis
Phishly respects user privacy by only analyzing emails that users explicitly choose to scan. This ensures that sensitive data remains confidential and only relevant information is processed, providing peace of mind for individuals and small businesses alike.
Use Cases
Perkoon
Media Production & Creative Agencies
Teams regularly exchanging multi-gigabyte raw video footage, design files, and final renders between editors, clients, and external partners can utilize free P2P transfers for instantaneous review cycles. Cloud storage holds deliverables for client download on their schedule, eliminating costly overages from traditional transfer services and accelerating project timelines.
Software Development & DevOps
Development teams can integrate Perkoon's CLI and API into their deployment pipelines to automatically transfer build artifacts, log files, or database dumps between environments or to stakeholders. The native automation support ensures reliable, hands-off operation critical for agile development and continuous integration/continuous deployment (CI/CD) processes.
Legal & Financial Services Compliance
Firms handling sensitive client documents, audit trails, and confidential reports require secure transfer without third-party data mining. Perkoon's privacy-centric model, with encrypted cloud holds and P2P direct sends, provides a verifiable chain of custody and ensures that sensitive information remains protected throughout its lifecycle, supporting compliance mandates.
Enterprise IT & Infrastructure Management
IT departments can leverage Perkoon for cost-effective large-scale data distribution, such as deploying software packages, VM images, or backup archives across global offices. The ability to mix free P2P for internal transfers with on-demand cloud storage for external partners optimizes bandwidth costs and simplifies digital asset logistics.
Phishly
Individual Email Safety
Individuals can utilize Phishly to scan their personal emails for phishing attempts. By quickly assessing the safety of emails, users can avoid falling victim to scams and protect their personal information.
Small Business Email Security
Small businesses often face unique cybersecurity threats. Phishly equips small business owners with the necessary tools to detect phishing attempts in their business communications, safeguarding client relationships and company reputation.
Educational Institutions
Educational institutions can benefit from Phishly by training staff and students on identifying phishing emails. With Phishly, they can promote a culture of cybersecurity awareness and reduce the risk of compromised accounts.
Remote Workforce Protection
As remote work becomes increasingly common, Phishly provides an additional layer of security for employees working from home. By scanning emails for phishing indicators, remote workers can confidently navigate their inboxes without jeopardizing company data.
Overview
About Perkoon
Perkoon is a next-generation file transfer platform engineered for business efficiency and uncompromising data sovereignty. It eliminates the friction, cost overhead, and privacy concerns endemic to traditional cloud services by leveraging a dual-architecture model. The platform is designed for professionals, teams, and enterprises that require a reliable, scalable, and cost-predictable method for exchanging digital assets, from large multimedia files to sensitive project documents. Its core value proposition is a transparent, utility-based pricing model: unlimited, free peer-to-peer (P2P) transfers for real-time exchanges, and fairly priced encrypted cloud storage for asynchronous delivery. This approach directly translates to significant ROI by removing per-user seat licenses and arbitrary file size caps that cripple productivity. Furthermore, Perkoon is architected for the modern automation stack, offering native API access and AI-agent compatibility, positioning it as critical infrastructure for streamlined, automated workflows without the security risks of screen-scraping.
About Phishly
Phishly is an innovative AI-powered phishing detection platform designed specifically to enhance email security for individuals and small businesses. Available as a convenient Chrome extension for Gmail and as a web tool, Phishly simplifies the process of identifying potentially harmful emails. Users can easily scan emails by clicking "Scan with Phishly" in Gmail or by pasting suspicious emails on the Phishly website for immediate analysis. The platform employs advanced artificial intelligence to detect a variety of phishing indicators, including suspicious domains, urgent language, spoofed senders, and social engineering tactics. By providing clear and actionable risk assessments categorized as Safe, Medium Risk, or High Risk, Phishly empowers users to make informed decisions about their email interactions. This user-friendly solution offers a straightforward approach to phishing protection, eliminating the complexities often associated with enterprise-level cybersecurity tools. With a focus on privacy, Phishly only analyzes emails that users explicitly choose to scan, ensuring that sensitive information remains secure. Ideal for those seeking effective phishing protection without requiring technical expertise, Phishly delivers instant answers, thereby significantly enhancing productivity and peace of mind.
Frequently Asked Questions
Perkoon FAQ
How does Perkoon offer unlimited free P2P transfers?
The free P2P service is sustainable because it utilizes a direct connection between the sender's and recipient's web browsers. The file data never touches or is stored on Perkoon's servers, meaning the company incurs negligible infrastructure costs for this service. This cost-saving is passed directly to the user, allowing for truly unlimited, free transfers when both parties are online.
What happens if the recipient is not online when I send a file?
If the recipient is offline, the sender can opt to use Perkoon's Encrypted Cloud Storage. The file is securely uploaded and held on Perkoon's servers until the recipient is available to download it. This ensures guaranteed delivery. This is a paid feature, as it involves tangible server storage and bandwidth costs for Perkoon.
Is my data private and secure with Perkoon?
Yes. For P2P transfers, data is transmitted directly between browsers; Perkoon cannot see or access it. For files in cloud storage, they are encrypted at rest on Perkoon's servers. The company has a stated policy of no data scanning, analysis, or selling for advertising, ensuring your business data remains your own.
Can automated systems and AI agents use Perkoon?
Absolutely. Perkoon is designed for automation. It provides a native JavaScript API (window.__perkoon) accessible to browser-based AI agents and a Command Line Interface (CLI) tool. This allows scripts and autonomous agents to initiate and manage file transfers programmatically without the need for manual intervention or brittle screen-scraping techniques.
Phishly FAQ
How does Phishly detect phishing emails?
Phishly employs advanced artificial intelligence algorithms to analyze email content and identify common phishing indicators, including suspicious domains, urgent wording, and other red flags.
Is Phishly easy to use for non-technical users?
Yes, Phishly is designed with user-friendliness in mind. The interface is intuitive, allowing users with no technical background to easily scan and assess the safety of their emails.
Does Phishly compromise my email privacy?
No, Phishly prioritizes user privacy by only analyzing emails that you explicitly choose to scan. Your personal information remains secure and confidential throughout the scanning process.
Is Phishly free to use?
Phishly is free to use, making it an accessible tool for individuals and small businesses looking to enhance their email security without incurring costs or engaging in complex setups.
