CMMC ROI vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
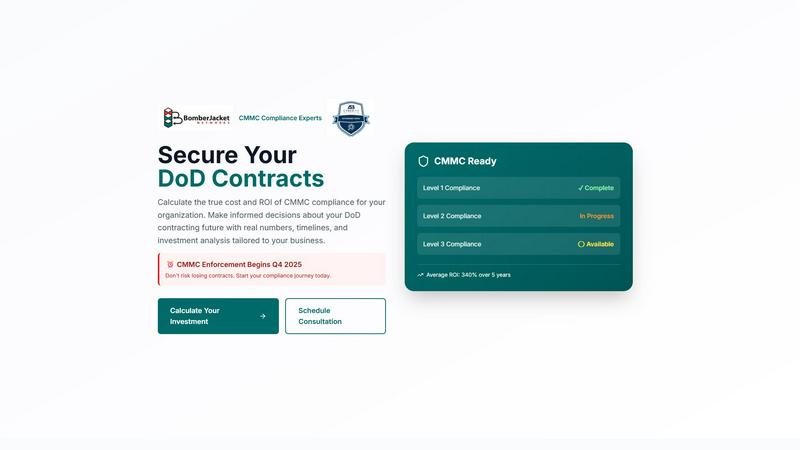
CMMC ROI
CMMC ROI calculates your compliance costs and investment returns to secure DoD contracts.
Last updated: March 1, 2026
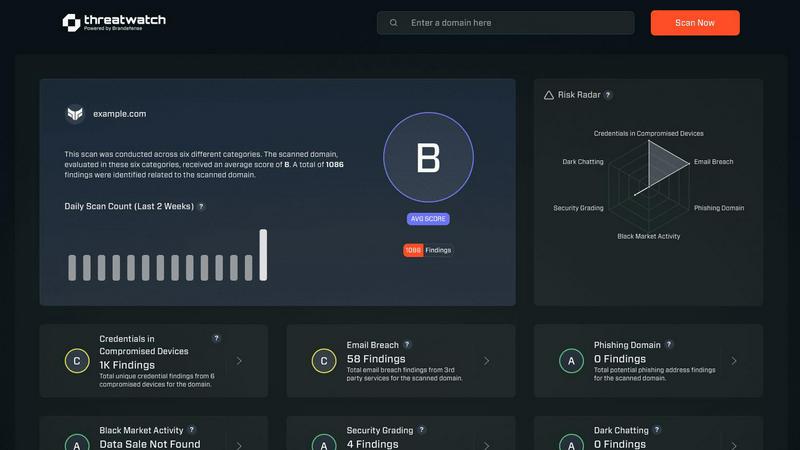
Threat Watch
Threat Watch delivers rapid insights into your cybersecurity health by identifying compromised accounts and critical.
Last updated: March 1, 2026
Visual Comparison
CMMC ROI
Threat Watch
Feature Comparison
CMMC ROI
Dynamic ROI Investment Calculator
The platform's core engine is a sophisticated, customizable calculator that models the complete financial picture of CMMC compliance. Users input specific variables such as company size, annual DoD revenue, target CMMC level, and current compliance status to receive a personalized analysis. It calculates the total 5-year investment range, projected ROI percentage, and the critical break-even timeline, providing an executive-level view of the compliance initiative's financial impact and value.
Scenario-Based Cost Modeling
CMMC ROI includes pre-loaded, real-world contractor scenarios (e.g., Small Contractor, Large Prime, Technology Firm) that provide immediate benchmark data. These quick-start examples illustrate investment ranges from $73K for a Level 1 FCI contractor to over $17M for a large Level 3 prime, offering context and a starting point for companies to gauge their own potential investment before personalizing their calculation.
CMMC Protection & Risk Assessment Dashboard
Beyond pure cost, the platform delivers a critical risk assessment dashboard. It quantifies the "Contract Value at Risk" (typically 100% without certification), models the average cost of a data breach or false claims penalty avoided ($2.5M), and projects the competitive advantage gained through increased bid win rates. This translates cybersecurity risk into clear business and financial terms for stakeholders.
Implementation Timeline Projector
The tool provides a detailed, phase-gated 12-month roadmap to CMMC Level 2 certification. It breaks down the journey from Gap Assessment and Remediation through Documentation and final Certification, assigning timeframes and milestones for each phase. This feature enables realistic project planning, resource allocation, and sets clear expectations for the path to audit readiness.
Threat Watch
Real-Time Monitoring
Threat Watch provides real-time monitoring of compromised credentials, allowing organizations to stay ahead of cyber threats. This feature ensures that businesses are alerted immediately when their sensitive information is at risk, enabling proactive measures to mitigate potential damage.
Comprehensive Risk Assessment
The platform delivers automated risk assessments across critical security categories, giving organizations a thorough understanding of their cybersecurity health. This comprehensive evaluation helps prioritize vulnerabilities, ensuring that resources are allocated effectively to areas that require immediate attention.
Dark Web Intelligence
With Threat Watch's dark web monitoring capabilities, organizations can uncover threats lurking in hidden corners of the internet. This feature tracks exposed data and compromised accounts, empowering businesses to take corrective actions before their information is exploited by cybercriminals.
Phishing Detection and Response
Threat Watch includes advanced phishing address monitoring, identifying potential phishing threats in real time. By alerting organizations to suspicious addresses and behaviors, this feature helps prevent financial losses and data breaches caused by phishing attacks.
Use Cases
CMMC ROI
Executive Budget Justification & Board Approval
CFOs, CEOs, and Board Members utilize CMMC ROI to secure funding for compliance initiatives. The platform generates an "Executive Briefing" with concrete ROI projections, payback periods, and risk quantification, transforming a complex security requirement into a defensible business investment case with clear financial returns and risk mitigation.
Strategic Bid/No-Bid Decision Support
Business development and capture teams use the tool to evaluate the profitability of pursuing specific DoD contracts. By calculating the compliance investment required against the potential contract revenue, organizations can make data-driven decisions on which opportunities to pursue, ensuring the cost of compliance does not erode contract margins.
Compliance Program Scoping & Roadmapping
IT Directors and CISOs employ CMMC ROI to scope the size, cost, and timeline of their compliance program. The personalized investment range and detailed implementation timeline allow for accurate internal budgeting, staffing plans, and vendor management, ensuring the compliance project is set up for success from the outset.
Mergers, Acquisitions, and Partnership Due Diligence
Companies evaluating the acquisition of, or partnership with, a DoD contractor use the platform to assess the target's CMMC readiness and associated financial liabilities. It helps quantify the potential investment needed to bring the entity into compliance, informing valuation and negotiation strategies.
Threat Watch
Enhancing Security Posture
Organizations can utilize Threat Watch to enhance their overall security posture. By continuously monitoring for vulnerabilities and exposures, businesses can implement timely measures to protect their assets and reduce their risk profile.
Incident Response Optimization
In the event of a security breach, Threat Watch enables IT teams to respond rapidly by providing real-time insights and assessments. This capability not only speeds up incident response times but also minimizes the impact of breaches on business operations.
Compliance and Regulatory Adherence
Companies can leverage Threat Watch to ensure compliance with industry standards and regulations. By maintaining a comprehensive overview of their cybersecurity health, organizations can demonstrate their commitment to protecting sensitive data and adhering to legal requirements.
Employee Training and Awareness
Threat Watch can be instrumental in employee training programs by providing insights into current threats, such as phishing attempts. By educating staff on these threats, organizations can foster a culture of cybersecurity awareness, reducing the likelihood of successful attacks.
Overview
About CMMC ROI
CMMC ROI is an enterprise-grade financial analysis and strategic planning platform developed by BomberJacket Networks, an authorized C3PAO and service-disabled veteran-owned business. It is designed exclusively for Department of Defense (DoD) contractors and subcontractors who must achieve Cybersecurity Maturity Model Certification (CMMC) to bid on and retain defense contracts. The platform's core value proposition is transforming CMMC compliance from a perceived cost center into a quantifiable strategic investment. By leveraging over two decades of cybersecurity expertise, CMMC ROI provides organizations with a data-driven model to calculate the true five-year total cost of ownership, projected return on investment (ROI), and precise payback period for their compliance journey. This empowers business leaders to make informed, fiscally responsible decisions, secure their revenue pipeline ahead of CMMC enforcement in Q4 2025, and gain a decisive competitive edge by understanding the financial implications of certification.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution designed to equip organizations with the tools necessary to protect their digital assets. By providing a detailed analysis of critical security categories, Threat Watch empowers businesses to assess their cybersecurity posture effectively. This platform caters to enterprises of all sizes, enabling IT and security professionals to pinpoint vulnerabilities, exposures, and overall risk levels within their environments. The main value proposition of Threat Watch lies in its ability to deliver real-time insights coupled with automated assessments. This capability allows organizations to respond swiftly and effectively to potential threats, thereby minimizing the risk of data breaches and other cybersecurity incidents. Key features include monitoring for compromised credentials, breached accounts, phishing addresses, and dark web contents, all of which contribute to a unified approach to cybersecurity that not only enhances productivity but also improves return on investment (ROI) for organizations.
Frequently Asked Questions
CMMC ROI FAQ
What is the basis for the ROI calculation?
The ROI calculation is derived from a standardized business formula: ROI = (Protected Value - Total Investment) / Total Investment x 100. Protected Value includes your 5-year DoD contract revenue at risk plus an average avoided cost of $2.5M for a potential breach or false claims incident. Total Investment sums the implementation cost, five years of maintenance, and one recertification event over a 5-year period.
How accurate are the cost ranges provided?
The cost ranges are based on BomberJacket Networks' extensive experience as a C3PAO, reflecting real-world data from hundreds of assessments. They account for variables like company size, system complexity, and current compliance status. The ranges provide a reliable estimate, with the customizable calculator allowing you to refine figures based on your specific environment for a more precise projection.
What if my company is already working on CMMC compliance?
The calculator includes "Progress Discounts" to account for work already completed. If your program is "In Progress," the model applies a 30% reduction to the implementation cost estimate. If you are "Nearly Complete," a 60% discount is applied. This ensures your ROI projection reflects your actual remaining investment, not the total cost from scratch.
Why is the payback period often less than one year?
The payback period is typically short because the "Protected Value" includes 100% of your near-term DoD contract revenue that would be lost without certification. For a contractor with active bids or recurring contracts, securing that revenue stream by achieving CMMC compliance results in a rapid return on the initial investment, often within the first contract cycle.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for enterprises of all sizes, from small businesses to large corporations. Any organization seeking to enhance its cybersecurity posture and protect its digital assets can benefit from this solution.
How does Threat Watch monitor dark web contents?
Threat Watch employs advanced algorithms and intelligence sources to monitor the dark web for compromised credentials and other sensitive information. This proactive approach helps organizations identify threats before they can be exploited.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to integrate seamlessly with a variety of existing security tools and platforms. This ensures that organizations can enhance their cybersecurity efforts without disrupting their current workflows.
How quickly can I expect to see results from Threat Watch?
Organizations can expect to see results almost immediately upon implementation. The real-time monitoring and automated assessments provided by Threat Watch deliver actionable insights that can help improve cybersecurity health from day one.
Alternatives
CMMC ROI Alternatives
CMMC ROI is a specialized business intelligence platform designed to help defense contractors calculate the financial costs and return on investment associated with achieving Cybersecurity Maturity Model Certification (CMMC). It provides a data-driven framework for making strategic compliance decisions. Organizations may explore alternatives for various reasons, including budget constraints, the need for different feature sets, or a preference for a platform that integrates with existing enterprise IT and security stacks. The specific scale of a contractor's operations and their internal resource availability also drive the search for a tailored solution. When evaluating any alternative, key considerations should include the depth of its ROI modeling, the provider's direct expertise in the CMMC framework and DoD contracting, and the solution's ability to deliver a clear, actionable compliance roadmap. The goal is to select a tool that translates complex security requirements into tangible business outcomes.
Threat Watch Alternatives
Threat Watch is an advanced cybersecurity intelligence solution designed to help organizations assess and enhance their digital security posture. Positioned within the realm of business intelligence, it provides actionable insights that enable users to monitor their cybersecurity health effectively. Organizations frequently seek alternatives to Threat Watch due to various factors such as pricing, specific feature sets, or compatibility with existing platforms. When exploring alternatives, it is crucial to consider the comprehensiveness of monitoring capabilities, ease of integration, and the ability to deliver real-time insights tailored to organizational needs. The right alternative should not only address immediate cybersecurity concerns but also offer scalability to adapt to future changes. Users should prioritize platforms that provide automated risk assessments, extensive credential monitoring, and robust dark web surveillance. Additionally, considering the user interface and customer support services can significantly impact the overall experience and effectiveness of the chosen solution.
