Pro Cursor Rules vs RedVeil
Side-by-side comparison to help you choose the right AI tool.
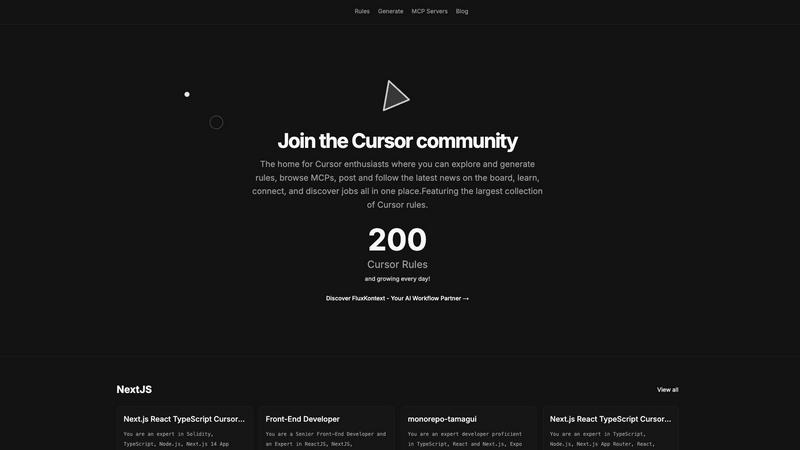
Pro Cursor Rules
Pro Cursor Rules centralizes AI-powered developer rules to boost team productivity and accelerate project delivery.
Last updated: February 28, 2026
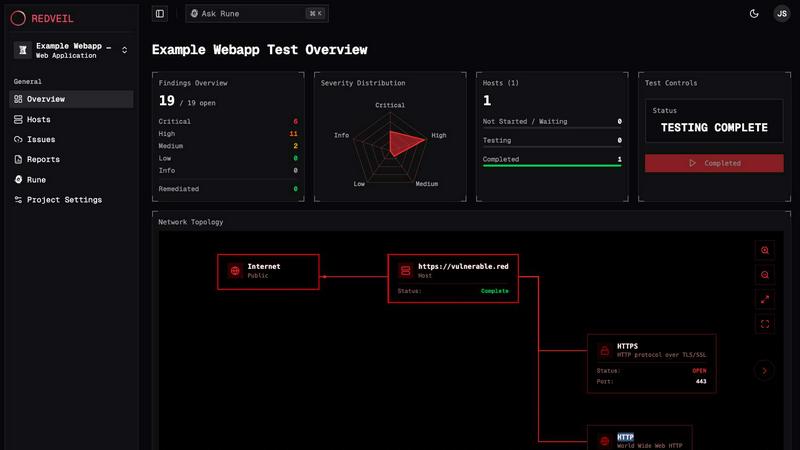
RedVeil
RedVeil delivers AI-powered penetration testing that uncovers vulnerabilities quickly and affordably with actionable.
Last updated: February 26, 2026
Visual Comparison
Pro Cursor Rules
RedVeil
Feature Comparison
Pro Cursor Rules
Curated Enterprise Rule Repository
The platform hosts the largest centralized collection of expert-vetted Cursor Rules, covering leading frameworks and technologies like Next.js 14 App Router, React, TypeScript, Supabase, and Tailwind CSS. Each rule is a comprehensive set of AI instructions that encapsulate senior-level expertise, ensuring generated code adheres to modern best practices, security standards, and optimal architectural patterns right from the first prompt, eliminating guesswork and inconsistency.
AI-Powered Rule Generation Engine
Beyond browsing, the platform provides intelligent tools to generate custom, project-specific Cursor Rules. This feature allows teams to codify their unique internal standards, proprietary patterns, and company-specific architectural decisions directly into their AI workflow, ensuring the assistant acts as a true extension of the team's knowledge base and enforcing governance automatically across all developers.
Integrated MCP Server Hub
Pro Cursor Rules extends functionality by providing access to and information about Model Context Protocol (MCP) servers. This integration allows developers to seamlessly connect their Cursor editor to external data sources, tools, and APIs, transforming the AI assistant into a central command center that can interact with databases, design systems, and internal documentation, thereby unlocking advanced, context-rich development capabilities.
Collaborative Community & Knowledge Sharing
The platform is built around a vibrant community hub where developers and teams can share, rate, and discuss rules. This social layer accelerates collective learning, allows teams to discover and adopt industry-proven patterns quickly, and provides a channel for news, networking, and professional opportunities, fostering an ecosystem of continuous improvement and shared expertise.
RedVeil
Speed & Efficiency
RedVeil dramatically reduces the time required for penetration testing from weeks to mere hours. Organizations can initiate tests on demand, ensuring that security assessments align seamlessly with rapid development cycles, thereby avoiding delays in deployment.
Comprehensive Reporting
With RedVeil, users receive audit-ready reports that cater to various stakeholders, including executives, engineers, and compliance teams. This feature ensures that findings are presented in a professional format, ready for SOC 2, ISO 27001, PCI-DSS, and other compliance frameworks.
Guided Remediation
RedVeil offers contextual insights into vulnerabilities, providing users with clear reproduction steps and guidance on how to resolve issues. This feature empowers teams to address security flaws effectively and enhances overall security posture.
Flexibility & Customization
The platform allows organizations to tailor their testing schedules and scope based on their unique needs. This flexibility ensures that businesses can conduct regular assessments without the constraints of traditional testing schedules, adapting to changes in their environments as necessary.
Use Cases
Pro Cursor Rules
Standardizing Output Across Engineering Teams
Engineering leaders can deploy a standardized set of curated rules for their primary tech stack (e.g., Next.js, TypeScript, Tailwind) to ensure every developer, regardless of seniority, produces code that follows identical patterns, naming conventions, and architectural guidelines. This directly reduces code review burden by up to 40% and creates a consistent, maintainable codebase, crucial for scaling teams and long-term project health.
Accelerating New Developer Onboarding
Instead of weeks of manual mentorship and documentation review, new hires can be equipped with the team's specific Cursor Rules on day one. This instantly aligns them with the project's standards and patterns, allowing them to contribute production-ready code immediately. This use case dramatically shortens the onboarding ramp-up time, translating to faster time-to-productivity and significant cost savings.
Enforcing Architectural Governance & Best Practices
For organizations committed to specific architectural decisions (like using App Router, Shadcn UI, or a particular state management solution), rules act as an enforceable policy layer. The AI assistant will guide developers toward the approved tools and patterns while steering them away from anti-patterns, ensuring architectural integrity and reducing technical debt from the outset of every new feature or module.
Rapid Prototyping and Boilerplate Generation
Development teams can leverage technology-specific rules to generate entire feature scaffolds, configuration files, and complex component logic with expert-level structure in seconds. This eliminates the repetitive, low-value work of setting up projects, configuring libraries like Supabase or Stripe, or writing boilerplate code, allowing developers to focus their intellectual effort on solving unique business logic problems.
RedVeil
Continuous Integration/Continuous Deployment (CI/CD) Environments
In CI/CD workflows, where code changes are frequent, RedVeil enables teams to run penetration tests at any stage of development. This ensures that vulnerabilities are identified and addressed promptly, reducing the risk of security issues in production.
Compliance and Regulatory Requirements
Organizations subject to regulatory standards such as PCI-DSS or ISO 27001 can utilize RedVeil to generate compliance-ready reports. This capability simplifies the audit process and helps maintain adherence to necessary security protocols.
Software Development Companies
For software development teams, RedVeil serves as a valuable tool to enhance security during the development lifecycle. By integrating penetration testing into their processes, teams can identify and remediate vulnerabilities before product releases, ensuring higher quality and security.
Incident Response Preparation
RedVeil assists organizations in preparing for potential security incidents by simulating real-world attack scenarios. This proactive approach enables teams to understand potential attack paths and develop robust incident response strategies, enhancing overall security readiness.
Overview
About Pro Cursor Rules
Pro Cursor Rules is the definitive enterprise-grade platform and community hub engineered for development teams and engineering leaders who leverage the Cursor AI code editor. It addresses a critical gap in AI-assisted development by transforming the generic AI pair programmer into a specialized, context-aware team member aligned with your specific technology stack and architectural standards. The platform's core is a vast, curated, and shareable repository of "Cursor Rules"—pre-configured AI agent instructions that codify coding standards, framework-specific best practices, and architectural patterns for technologies like Next.js, React, TypeScript, Supabase, Tailwind CSS, and beyond. This centralized knowledge base serves as a collaborative ecosystem, enabling teams to standardize output, enforce governance, and dramatically accelerate onboarding and development velocity. For engineering leadership, the value proposition is clear and measurable: a direct ROI through significant reductions in boilerplate coding, minimized code review cycles, enforced consistency, and the elimination of costly context-switching. Pro Cursor Rules is not merely a tool; it is a strategic asset for systematically harnessing AI to improve software quality, team efficiency, and predictable delivery at scale.
About RedVeil
RedVeil is an advanced AI-powered penetration testing solution designed to meet the rapid security needs of modern engineering teams. In a landscape where software is deployed daily, traditional penetration testing methods, which often take weeks and cost tens of thousands of dollars, are no longer sufficient. RedVeil revolutionizes the pentesting process by combining the strategic reasoning of a human hacker with the unmatched speed of software. With RedVeil, organizations can initiate a full, autonomous penetration test within minutes and receive a comprehensive, actionable report by the end of the day. This innovative approach not only enhances security but also offers significant cost savings, making it ideal for businesses of all sizes that prioritize continuous testing and compliance.
Frequently Asked Questions
Pro Cursor Rules FAQ
What exactly is a "Cursor Rule"?
A Cursor Rule is a detailed set of instructions and context provided to the Cursor AI editor's underlying language model. It defines your preferred coding standards, architectural patterns, technology choices, and stylistic preferences. Think of it as a specialized "persona" or guide that transforms the general-purpose AI into a senior developer expert in your specific stack, ensuring every code suggestion and generation aligns perfectly with your team's requirements.
How does Pro Cursor Rules ensure the quality of its shared rules?
The platform operates on a community-driven model with curation. Rules are often created and shared by experienced developers and industry experts. Users can browse, try, and rate rules, with the most effective and popular ones rising to prominence. This social proof mechanism, combined with the platform's focus on enterprise-grade content, creates a repository where quality is continuously validated and improved by the community itself.
Can I create and use private rules for my company?
Yes, a core value proposition of Pro Cursor Rules is the ability to generate and manage custom, private rules. This allows your engineering team to codify proprietary patterns, internal APIs, and company-mandated security or style guidelines into your AI workflow. These private rules ensure your competitive advantages and internal knowledge remain secure while still leveraging the platform's generation and management tools.
Do I need to be an expert to use or create rules?
Not at all. While creating highly sophisticated rules benefits from deep expertise, the platform is designed to be accessible. Developers can immediately browse and apply existing rules from the vast public library with a single click. Furthermore, the rule generation tools guide users in structuring their instructions, making it straightforward for team leads to encapsulate their key standards without needing to be prompt engineering experts.
RedVeil FAQ
Does RedVeil perform a real penetration test?
Yes, RedVeil conducts genuine penetration tests using AI-driven technology to identify and analyze vulnerabilities in your systems, providing actionable insights and remediation guidance.
How many penetration tests can I do with my annual subscription?
The number of tests you can conduct depends on the specific plan you choose. RedVeil offers different tiers, allowing you to select a plan that best fits your testing needs and budget.
Is there a chance that my web application or network could go down during the test?
RedVeil is designed to minimize disruption. However, as with any penetration testing, there is always a slight risk of affecting performance. It is advisable to conduct tests during off-peak hours or in a controlled environment.
Can I use RedVeil's penetration test reports to meet the requirements of my compliance?
Absolutely. RedVeil generates audit-ready reports that align with various compliance standards, making it easier for organizations to demonstrate their security posture to auditors and stakeholders.
Alternatives
Pro Cursor Rules Alternatives
Pro Cursor Rules is the definitive enterprise platform for developers and engineering teams using the Cursor AI code editor. It functions as a centralized hub for sharing and discovering AI-powered rules, which are pre-configured instructions that transform the AI assistant into a specialized, context-aware team member. This category focuses on maximizing developer productivity, enforcing code consistency, and accelerating development velocity through structured AI guidance. Users may explore alternatives for various strategic reasons. Common drivers include budget constraints, specific feature requirements not met by the core offering, or a need for a different deployment model. Some teams might seek solutions with a different focus, such as more granular integration capabilities or alternative community-driven approaches to rule curation and sharing. When evaluating alternatives, key considerations should align with core business objectives. Prioritize solutions that demonstrably improve team efficiency and code quality. Assess the depth and relevance of the rule library to your tech stack, the flexibility for customization, and the platform's ability to scale with your team. The ultimate goal is to secure a measurable return on investment through reduced boilerplate, faster onboarding, and enforced architectural governance.
RedVeil Alternatives
RedVeil is an innovative solution in the realm of penetration testing, leveraging agentic AI to deliver on-demand security assessments. As organizations increasingly adopt agile methodologies and deploy code at a rapid pace, traditional penetration testing methods can become cumbersome and costly. Users commonly seek alternatives to RedVeil for various reasons, including pricing concerns, feature sets that may better fit specific platform needs, or a desire for enhanced customization in their security testing processes. When selecting an alternative to RedVeil, it is crucial to consider factors such as the speed of testing, the depth of analysis provided, and the overall cost-effectiveness. Additionally, look for solutions that offer flexible scheduling and comprehensive reporting capabilities, ensuring that the chosen alternative aligns with your organization's security requirements and operational workflows.
