iGPT vs Threat Watch
Side-by-side comparison to help you choose the right AI tool.
iGPT converts email data into secure, actionable insights to boost productivity and streamline enterprise workflows.
Last updated: February 28, 2026
Threat Watch
Threat Watch delivers rapid insights into your cybersecurity health by identifying compromised accounts and critical.
Last updated: March 1, 2026
Visual Comparison
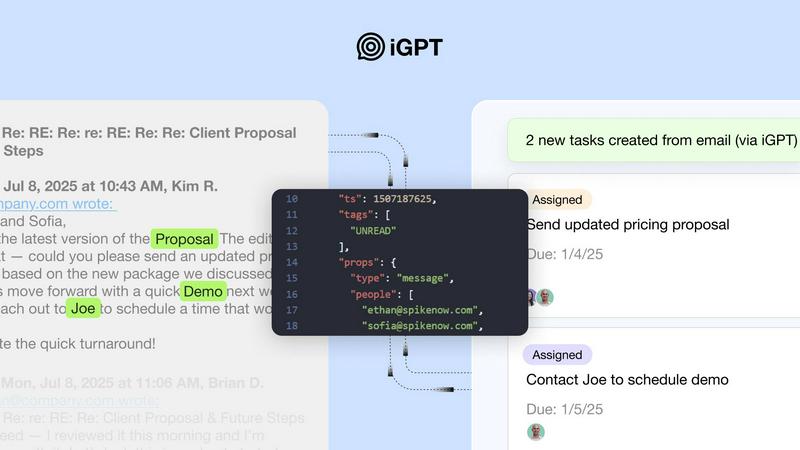
iGPT
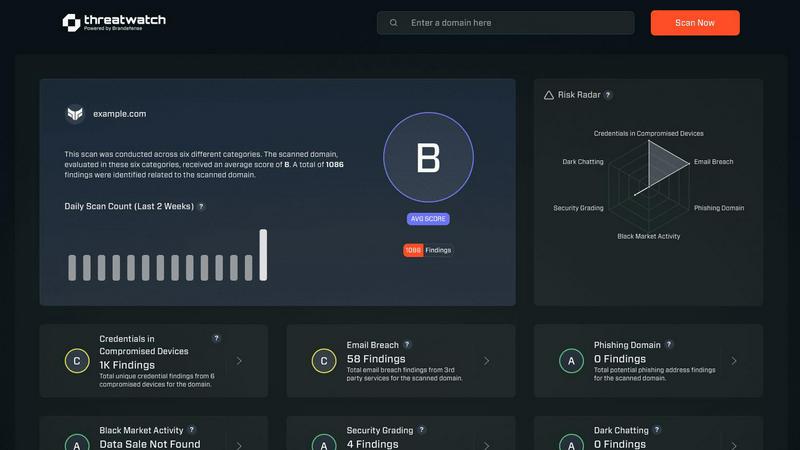
Threat Watch
Feature Comparison
iGPT
Immediate Integration
iGPT offers an SDK and live playground for rapid testing of requests and responses. This allows businesses to quickly integrate the API into their existing systems, ensuring a smooth transition and minimal disruption to workflows.
Contextual Responses
The API provides context-aware answers that are ready for reasoning and automation. Each response is linked back to the source, ensuring transparency and reliability in the information provided, which is crucial for effective decision-making.
Realtime Ingestion
With iGPT, new messages and attachments are indexed instantly, ensuring that the data is always up-to-date. This feature allows organizations to act on the latest information without delay, enhancing productivity and responsiveness.
Compliance and Audit Trail
iGPT ensures that data remains under the control of the organization with full audit trails. This feature allows companies to trace feedback, approvals, and rationale back to original conversations, maintaining compliance and accountability.
Threat Watch
Real-Time Monitoring
Threat Watch provides real-time monitoring of compromised credentials, allowing organizations to stay ahead of cyber threats. This feature ensures that businesses are alerted immediately when their sensitive information is at risk, enabling proactive measures to mitigate potential damage.
Comprehensive Risk Assessment
The platform delivers automated risk assessments across critical security categories, giving organizations a thorough understanding of their cybersecurity health. This comprehensive evaluation helps prioritize vulnerabilities, ensuring that resources are allocated effectively to areas that require immediate attention.
Dark Web Intelligence
With Threat Watch's dark web monitoring capabilities, organizations can uncover threats lurking in hidden corners of the internet. This feature tracks exposed data and compromised accounts, empowering businesses to take corrective actions before their information is exploited by cybercriminals.
Phishing Detection and Response
Threat Watch includes advanced phishing address monitoring, identifying potential phishing threats in real time. By alerting organizations to suspicious addresses and behaviors, this feature helps prevent financial losses and data breaches caused by phishing attacks.
Use Cases
iGPT
Email Assistants
iGPT enables the development of email assistants that can draft, prioritize, and act on emails with complete contextual understanding. This enhances productivity by reducing the time spent on email management.
Workflow Automation
Businesses can leverage iGPT to transform email threads into actionable tasks, deadlines, and approvals. This capability flags bottlenecks in processes, ensuring that workflows remain efficient and on track.
Support Copilots
iGPT can help rebuild the entire customer narrative across lengthy email chains, attachments, and tone shifts. This ensures that support teams have a comprehensive view of customer interactions, leading to better service and resolution times.
Insights from Attachments
The API allows for the summarization of invoices, contracts, and files within the context of email threads and participants. This feature streamlines information retrieval and enhances decision-making based on comprehensive insights.
Threat Watch
Enhancing Security Posture
Organizations can utilize Threat Watch to enhance their overall security posture. By continuously monitoring for vulnerabilities and exposures, businesses can implement timely measures to protect their assets and reduce their risk profile.
Incident Response Optimization
In the event of a security breach, Threat Watch enables IT teams to respond rapidly by providing real-time insights and assessments. This capability not only speeds up incident response times but also minimizes the impact of breaches on business operations.
Compliance and Regulatory Adherence
Companies can leverage Threat Watch to ensure compliance with industry standards and regulations. By maintaining a comprehensive overview of their cybersecurity health, organizations can demonstrate their commitment to protecting sensitive data and adhering to legal requirements.
Employee Training and Awareness
Threat Watch can be instrumental in employee training programs by providing insights into current threats, such as phishing attempts. By educating staff on these threats, organizations can foster a culture of cybersecurity awareness, reducing the likelihood of successful attacks.
Overview
About iGPT
iGPT is a sophisticated email intelligence API designed to revolutionize how enterprises manage and interact with their email and communication data. By functioning as a secure and auditable gateway for AI-driven systems, iGPT allows organizations to extract valuable insights from email conversations and attachments. Its capabilities extend beyond basic data retrieval, delivering context-aware answers that are pivotal for informed decision-making in real time. Tailored for businesses that demand reliable and efficient workflows, iGPT offers immediate integration, contextual responses, and flexible deployment options. The primary value proposition of iGPT lies in its ability to enhance communication processes, boost productivity, and ensure compliance while safeguarding sensitive information. This makes it an indispensable tool for enterprises aiming to optimize their email interactions and elevate operational efficiency.
About Threat Watch
Threat Watch is a state-of-the-art cybersecurity intelligence solution designed to equip organizations with the tools necessary to protect their digital assets. By providing a detailed analysis of critical security categories, Threat Watch empowers businesses to assess their cybersecurity posture effectively. This platform caters to enterprises of all sizes, enabling IT and security professionals to pinpoint vulnerabilities, exposures, and overall risk levels within their environments. The main value proposition of Threat Watch lies in its ability to deliver real-time insights coupled with automated assessments. This capability allows organizations to respond swiftly and effectively to potential threats, thereby minimizing the risk of data breaches and other cybersecurity incidents. Key features include monitoring for compromised credentials, breached accounts, phishing addresses, and dark web contents, all of which contribute to a unified approach to cybersecurity that not only enhances productivity but also improves return on investment (ROI) for organizations.
Frequently Asked Questions
iGPT FAQ
What types of businesses can benefit from iGPT?
iGPT is designed for enterprises across various industries that rely heavily on email communication for workflows. This includes sectors such as finance, legal, customer service, and project management, where efficient email management is crucial.
How secure is the data processed through iGPT?
iGPT employs enterprise-grade security measures, including zero data training, role-based access control, and zero data retention. This ensures that sensitive information remains protected and under the company’s control at all times.
Is iGPT easy to integrate with existing systems?
Yes, iGPT provides an SDK and a live playground that simplifies the integration process. This allows organizations to quickly implement the API without significant disruptions to their existing workflows.
Can iGPT handle large volumes of email data?
Absolutely. iGPT is designed to manage large and complex datasets efficiently. Its real-time ingestion and hybrid retrieval capabilities ensure that organizations can extract relevant insights quickly, even from vast amounts of email data.
Threat Watch FAQ
What types of organizations can benefit from Threat Watch?
Threat Watch is designed for enterprises of all sizes, from small businesses to large corporations. Any organization seeking to enhance its cybersecurity posture and protect its digital assets can benefit from this solution.
How does Threat Watch monitor dark web contents?
Threat Watch employs advanced algorithms and intelligence sources to monitor the dark web for compromised credentials and other sensitive information. This proactive approach helps organizations identify threats before they can be exploited.
Can Threat Watch integrate with existing security tools?
Yes, Threat Watch is designed to integrate seamlessly with a variety of existing security tools and platforms. This ensures that organizations can enhance their cybersecurity efforts without disrupting their current workflows.
How quickly can I expect to see results from Threat Watch?
Organizations can expect to see results almost immediately upon implementation. The real-time monitoring and automated assessments provided by Threat Watch deliver actionable insights that can help improve cybersecurity health from day one.
Alternatives
iGPT Alternatives
iGPT is an innovative email intelligence API that falls under the category of business intelligence solutions. It is designed to transform email data into secure, context-aware insights, thereby enhancing productivity within enterprise workflows. Users often seek alternatives to iGPT for various reasons, including pricing, specific feature sets, or compatibility with existing platforms. The need for customization, scalability, and unique functionalities can also drive the search for alternatives. When exploring alternatives to iGPT, it's essential to consider several factors. Look for solutions that offer seamless integration capabilities, robust security features, and the ability to provide contextually relevant responses. Additionally, evaluate the ease of use, support options, and whether the alternative can meet your organization’s specific communication and data management needs.
Threat Watch Alternatives
Threat Watch is an advanced cybersecurity intelligence solution designed to help organizations assess and enhance their digital security posture. Positioned within the realm of business intelligence, it provides actionable insights that enable users to monitor their cybersecurity health effectively. Organizations frequently seek alternatives to Threat Watch due to various factors such as pricing, specific feature sets, or compatibility with existing platforms. When exploring alternatives, it is crucial to consider the comprehensiveness of monitoring capabilities, ease of integration, and the ability to deliver real-time insights tailored to organizational needs. The right alternative should not only address immediate cybersecurity concerns but also offer scalability to adapt to future changes. Users should prioritize platforms that provide automated risk assessments, extensive credential monitoring, and robust dark web surveillance. Additionally, considering the user interface and customer support services can significantly impact the overall experience and effectiveness of the chosen solution.
